"...what is art? Privacy exposed to radiant light."
— Mu Xin, Chinese Landscape Painter
Undef, User 632 (2013). Animated GIF documentation of real-time visualization of data collected from passersby.
A collection of items from the Prosthetic Knowledge Tumblr archive and around the Web around the theme of privacy and surveillance. The projects listed below are tied to these themes in different ways: some take positions or raise questions on the new technological environments, some offer solutions for a world in which "just like the animals, we need to start adapting new ways to conceal ourselves from the autocratic predators" [source], while others collect and re-purpose ambient data in creative ways.
User 632 by Undef

Installation in a public window by Swiss design and physical computing studio Undef uses a Kinect sensor to collect data from its audience:
User 632 is an installation that stores the behaviour of the people who look at it by monitoring them in return. It wants to know when and how a person passes by or if they stop on the way.All data is being tracked and displayed publicly. Passers-by are stored as an anonymous number without any hints to their identities. Whoever comes to close to the camera though will be stored with a photograph next to their id.
The installation is made up of three Kinect depth cameras that constantly look for movements which are then reduced to a simple directional line in space. When a visitor enters a specific area, the algorithm is looking for a face. As soon as one is found a countdown appears that shows the time until a photo is taken automatically. At the same time the time a user is in the visible area is stored.
This data (time, path and eventually image) are stored in a database, interpreted and displayed as real-time statistics.
Inti Romero



Online identity performance comprising a public Facebook profile with personal photographs that are censored via pixelation. The project also offers an app with which to make your own censored photographs for sharing on social networks.
Desire of Codes by Seiko Mikami

Audiovisual installation by Seiko Mikami that uses robotic cameras to capture video of visitors which are then projected onto a hexagon "eye":
The "individual" visitor in a double role as a subject of expression and observation
This interactive installation consisting of three parts is set up in YCAM’s Studio A, a space that is normally used for theatre performances.
A large number of devices resembling tentacles with built-in small cameras are placed across a huge wall (Part 1), while six robotic “search arms” equipped with cameras and projectors are suspended from the ceiling (Part 2). Each device senses with insect-like wriggling movements the positions and movements of visitors, and turns toward detected persons in order to observe their actions. In addition, a giant round-shaped screen that looks like an insect’s compound eye is installed in the back of the exhibition space (Part 3). Visual data transmitted from each camera, along with footage recorded by surveillance cameras installed at various places around the world, are stored in a central database, and ultimately projected in complex images mixing elements of past and present, the venue itself and points around the globe, onto the screen. The compound eye visualizes a new reality in which fragmentary aspects of space and time are recombined, while the visitor’s position as a subject of expression and surveillance at once indicates the new appearances of human corporeality and desire.
More from the artist’s website here.
Anti Facial Recognition Visor

This is the world’s first pair of glasses which prevent facial recognition by cameras. They are currently under development by Japan’s National Institute of Informatics.
Photos taken without people’s knowledge can violate privacy. For example, photos may be posted online, along with metadata including the time and location. But by wearing this device, you can stop your privacy from being infringed in such ways.
“You can try wearing sunglasses. But sunglasses alone can’t prevent face detection. Because face detection uses features like the eyes and nose, it’s hard to prevent just by concealing your eyes. This is the privacy visor I have developed, which uses 11 near-infrared LEDs. I’m switching it on now. It prevents face detection, like this.”
“Light from these near-infrared LEDs can’t be seen by the human eye, but when it passes through a camera’s imaging device, it appears bright. The LEDs are installed in these locations because, a feature of face detection is, the eyes and part of the nose appear dark, while another part of the nose appears bright. So, by placing light sources mostly near dark parts of the face, we’ve succeeded in canceling face detection characteristics, making face detection fail.”
Compared with previous ways of physically hiding the face, this technology can protect privacy without obstructing communication, as all users need to do is wear a pair of glasses.
ZXX by Sang Mun
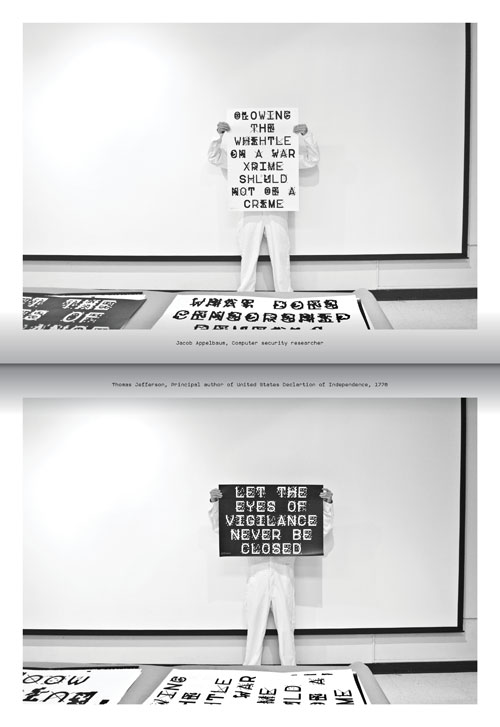
A font by Sang Mun designed to be unable to be read via OCR (Optical Character Recognition), protecting printed text to be captured with machine vision:
The name ZXX comes from the Library of Congress’ Alpha-3 ISO 639-2 — codes for the representation of names of languages. ZXX is used to declare No linguistic content; Not applicable.
Free Open Type Font to open up governments.
You can find out more (and download the font yourself) at the project’s page here.
The Pirate Cinema by Nicolas Maigret

In the context of omnipresent telecommunications surveillance, "The Pirate Cinema" makes the hidden activity and geography of Peer-to-Peer file sharing visible. The project is presented as a monitoring room, which shows Peer-to-Peer transfers happening in real time on networks using the BitTorrent protocol. The installation produces an arbitrary cut-up of the files currently being exchanged. This immediate and fragmentary rendering of digital activity, with information concerning its source and destination, thus depicts the topology of digital media consumption and uncontrolled content dissemination in a connected world.
Interactive Robotic Painting Machine (2011) by Benjamin Grosser
This is interesting on so many levels - the machine paints abstractly, the sounds it makes are amplified and used by the robot to make creative decisions, plus there is a camera where the brush is, offering an intimate birds-eye point of view on the painting process:
This machine uses artificial intelligence to paint its own body of work and to make its own decisions. While doing so, it listens to its environment and considers what it hears as input into the painting process. In the absence of someone or something else making sound in its presence, the machine, like many artists, listens to itself.
bengrosser.com
bengrosser.com/projects/interactive-robotic-painting-machine/
Other mentions:
Rhizome featured artist Adam Harvey's anti-drone clothing Stealth Wear.
Hell Is Other People: App which uses Foursquare data to find optimum space to avoid your friends.
Just for fun ... a spy programme name generator.